Creating an SSH server (Linux)
Table of Contents
- Install OpenSSH Server
- Configure your client
- Optional: add private key to ssh-agent
- Recommended configuration on the server
- Connect to your server
- More settings inside /etc/ssh/sshd_config
- Troubleshooting
If you are using a Linux VPS, you are connecting to it via SSH protocol. But if you have created a new user and you want to allow SSH access for that user, you will have to complete some simple steps.
On the other hand, if you have just created your own server but you don’t have SSH enabled, it will be also easy to do.
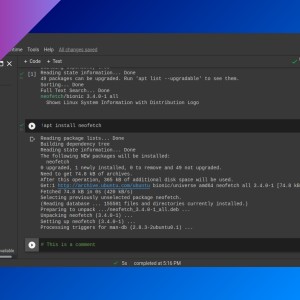
Install OpenSSH Server
- If SSH is not installed on your server, install
openssh. In Ubuntu, type this command (you need to be root or usesudo):
apt install openssh-server -yConfigure your client
- In your client, install
openssh-clientand look for a.ssh/folder in your home directory. If it doesn’t exists, create it and change its permissions so only the owner can access this folder.
mkdir ~/.ssh
chmod 700 ~/.ssh- Execute
ssh-keygencommand to create the private and public keys and select default values pressing Intro key (you can set a password for the private key if you want). Use-tparameter to specify the key type:rsa,ed25519, etc. On most systems, omiting the parameter creates an RSA key pair.
$ ssh-keygen -t rsa
Generating public/private rsa key pair.
Enter file in which to save the key (/home/user/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /home/user/.ssh/id_rsa
Your public key has been saved in /home/user/.ssh/id_rsa.pub
...- If you lose your public key, you can regenerate it:
ssh-keygen -y -f my-private-key.pem > my-public-key.pub- You can also specify an output directory and filename with
-f:
ssh-keygen -f /home/ricardo/ssh-keys/id_rsa- Run this command to copy the public key to the server.
ssh-copy-id -i ~/.ssh/id_rsa.pub <USER>@<SERVER_IP>- Now you can save your private key file in a secure place.
Optional: add private key to ssh-agent
In your client, you can add the private key to ssh-agent so you don’t need to type it every time you want to connect to your server. You can also avoid typing the private key path by creating an SSH config file.
- First, start
ssh-agentin the background.
eval `ssh-agent -s`- Add your private key with
ssh-add.
ssh-add /path/to/privatekeyRecommended configuration on the server
- Check SSH config file:
/etc/ssh/sshd_config.- It’s a good practice changing SSH port (
Port 22). Password Authentication nodisallows connecting to the server without a private key (check that you can connect with the private key before restarting SSH).PermitRootLogin nodisallows root user to connect through SSH.
- It’s a good practice changing SSH port (
- If you have made changes to this file, restart SSH typing as root:
systemctl restart ssh
#or
systemctl reload sshConnect to your server
ssh -i <private key file> <name>@<server>ssh -i /path/to/mykey ricardo@10.0.2.15Check Using the SSH terminal client.
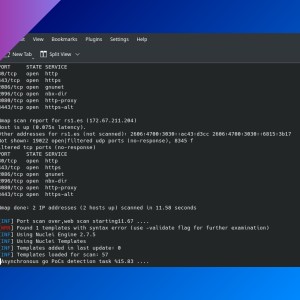
More settings inside /etc/ssh/sshd_config
X11Forwarding yesto allow X11 forwarding.- You may need to set
X11UseLocalhost noto allow remote X11 forwarding. DenyUsers <usernames>: you can deny users from connecting through SSH with this settings. Separate usernames by spaces.AllowUsers <usernames>: allow only specific users to connect through SSH. Separate usernames by spaces.AllowGroups <groups>: allow only specific groups to connect through SSH.ChrootDirectory <path>(e.g.:ChrootDirectory /home). Specifies the pathname of a directory to chroot to after authentication. At session startup sshd checks that all components of the pathname are root-owned directories which are not writable by any other user or group. The default is none, indicating not to chroot.- Check my post about SFTP to know how to restrict users to only use SFTP and not SSH.
LoginGraceTime <seconds>: the server disconnects after this time if the user has not successfully logged in.MaxSessions <number>: specifies the maximum number of open shell, login or subsystem (e.g. sftp) sessions permitted per network connection.
Troubleshooting
- I want to start the SSH server manually, without using systemd commands: run
which sshdto find where is the SSH server daemon, then run that file (e.g.:/usr/sbin/sshd). No host keys availableerror when sshd is started: openSSH hasn’t generated its keys automatically during installation. Runssh-keygen -Ainside/etc/ssh/(with superuser privileges).
If you have any suggestion, feel free to contact me via social media or email.
Latest tutorials and articles:
Featured content: