TCP Wrappers
Table of Contents
TCP Wrappers is a host-based ACL system you can use to fine-tuned access permissions for some services in your server.
Compatible services
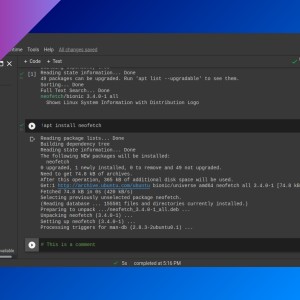
Some of those compatible services are: sshd, vsftpd, and nfs. You can find out which installed services are compatible with TCP Wrappers with lsof (this command lists open files, in this case it shows which current processes have opened a file. Run as root or use sudo):
lsof <libwrap library path>- libwrap library path may be different depending on the distribution. Some usual paths are:
/lib/x86_64-linux-gnu/libwrap.so.0/lib64/libwrap.so.0
hosts.allow and hosts.deny
Config files for TCP Wrappers are /etc/hosts.allow (for allowed hosts) and /etc/hosts.deny (for denied hosts). The syntax for both files is similar.
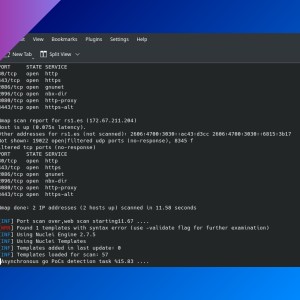
# /etc/hosts.deny
<service> : <hosts> : <options>- You can specify a service (
sshdfor example) or typeALLif that rule applies to all compatible services. <hosts>can be an IP address or hostname (or a comma-separated list). You can useALLas well.- You can specify a command to be executed when the rule is triggered (using
spawnand the command).
Rules on /etc/hosts.allow do not imply that hosts that do not appear in this file are not allowed. When a client wants to connect to the server, this happens:
- Service will check if this host is inside
hosts.allow. If it is, it won’t look further and will allow the connection. - If not, it will look inside
hosts.deny. If the host is inside this file, server won’t allow the client to connect. - If there is no deny rule that affects the client host, server will allow it to connect.
Examples
Some rule examples:
sshd : 172.0.0.5 : spawn /bin/echo `date` %c %d >> /var/log/ssh-logins/log- Use full paths for the command and when referring to files.
%cprints client info, like IP.%dprints service name.
If you have any suggestion, feel free to contact me via social media or email.
Latest tutorials and articles:
Featured content: