How to use Fail2Ban to restrict server access
Table of Contents
Fail2Ban scans log files, detects failed login attempts and performs actions like block IP addresses.
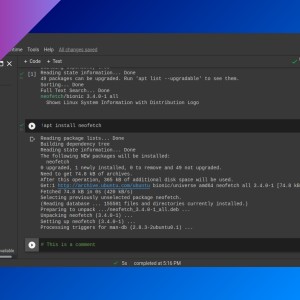
Installation
Install fail2ban package with your package manager (it’s available in most linux systems).
Usage
Fail2Ban has three main configuration file types:
- Filter: is a regular expression for a failed login. Fail2Ban will check log files for this.
- Action: action to perform.
- Jail: a combination of one filter and one or several actions.
Configuration files are inside /etc/fail2ban.
fail2ban-client is the frontend of Fail2Ban. It connects to the server socket and sends commands. In order to create or modify configuration files and run fail2ban-client you need superuser privileges.
Filters
Fail2Ban has several predefined filters (inside /etc/fail2ban/filter.d/) for popular services, like SSH, Apache, Nginx, etc.
Most important part on a filter file is the line that starts with fail-regex. This is where you add one or more regular expressions (one per line).
failregex = Authentication failure for .* from <HOST>
Failed [-/\w]+ for .* from <HOST>
ROOT LOGIN REFUSED .* FROM <HOST>
[iI](?:llegal|nvalid) user .* from <HOST><HOST> will match hostname or IP address of the user trying to log in.
Actions
There are also predefined actions (files inside /etc/fail2ban/action.d/). Most used is hostsdeny.conf, that will add user IP to /etc/hosts.deny.
Jails
Main configuration file is /etc/fail2ban/jail.conf but this file will be overwritten with every software update. You must create a file inside /etc/fail2ban/jail.d to define a jail or change jail defaults.
For example, you can create a sshd.conf file with this content.
[sshd]
enabled = true
filter = sshd
action = hostsdeny
maxretry = 3Check jail status
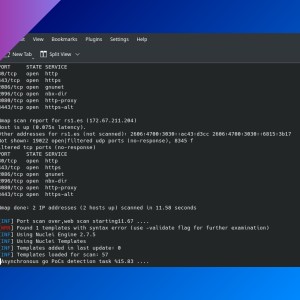
fail2ban-client status <jail>
# fail2ban-client status sshdUnban IP
fail2ban-client set <jail> unban <ip>
# fail2ban-client set sshd unban 10.0.2.15Check service status
fail2ban-client statusStart, stop and reload
Run fail2ban-client and start, stop or reload.
fail2ban-client reloadMore info
Check fail2ban --help or man fail2ban-client.
If you have any suggestion, feel free to contact me via social media or email.
Latest tutorials and articles:
Featured content: