Firejail: run apps inside a sandbox
Table of Contents
Firejail creates a restricted environment for untrusted applications. It’s written in C and it’s lightweight and easy to use.
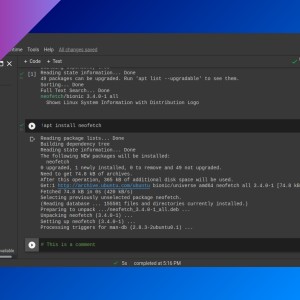
Installation
Firejail is available on most Linux-based operating systems (Debian, Arch Linux, etc.). Install firejail using your system package manager.
Creating sandboxes
firejail <options> <command>
# e.g.: firejail firefox- Without arguments, executes user preferred shell (specified in
$SHELL). In this case, exit from sandbox by typingexit(or press Ctrl + D). - Firejail does not work with Flatpak or Snap packages.
Some of the available options are:
--name=<name>: set a sanbox name.--net=none: no network access.--nosound: disable sound.--novideo: disable video devices such as the webcam.--private: mount new/rootand/home/userdirectories in temporary filesystems.--appimage <appimage file>: sandbox an AppImage.--disable-mnt: blacklist/mnt,/media,/run/mountand/run/mediaaccess.--blacklist=<folder or file path>: blacklist a folder or file.--private-bin=<file>,--private-etc=<file,directory>,--private-home=<file,directory>,--private-opt=<file,directory>,--private-srv=<file,directory>: create a new/bin,/etc,/homeor/optwith only the files and folders specified.--private-tmp: create an empty/tmp.--read-only=<folder or file path>: set directory or file read-only.
Run man firejail for more info.
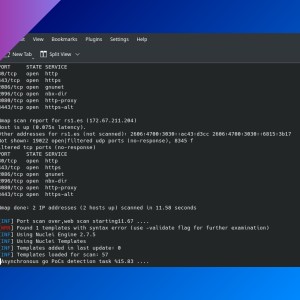
Monitoring and management
firejail --list: list sandboxes.firejail --top: top-like statistics.firejail --tree: print a tree of all sandboxed processes.firejail --shutdown=<name|pid>: shutdown a sandbox.firemon <pid>
Desktop integration
A symbolic link to /usr/bin/firejail under the name of a program, will start the program in Firejail sandbox. The symbolic link should be placed in the first $PATH position. On most systems, a good place is /usr/local/bin directory. For example (run as root or with ‘sudo’):
ln -s /usr/bin/firejail /usr/local/bin/firefoxVerify the right path for your app is the newly created:
$ which firefox
/usr/bin/firefox
$ sudo ln -s /usr/bin/firejail /usr/local/bin/firefox
$ which firefox
/usr/local/bin/firefoxWhen you don’t need to sandbox the application anymore, just delete the symbolic link (run as root or with ‘sudo’):
rm /usr/local/bin/firefoxIf you have any suggestion, feel free to contact me via social media or email.
Latest tutorials and articles:
Featured content: